Vision for Cybersecurity in the Medical Technology
In today’s dynamic healthcare landscape, fortifying the healthcare system against cyber threats like malware and ransomware attacks is pivotal. Ensuring cybersecurity is paramount across the medical industry, including biotechnology firms, insurers, healthcare providers, pharmaceutical companies, and medical device manufacturers. Also, it encompasses a range of measures to protect organizations from internal and external cyber-attacks, maintain uninterrupted medical services, preserve data confidentiality, ensure the optimal functioning of medical systems, safeguard patient information integrity, and comply with industry regulations. In this blog, we will delve into the crucial importance of healthcare cybersecurity and medical device cybersecurity (MedTech). Moreover, we’ll explore the multifaceted aspects of the proactive steps undertaken and the vision to safeguard the integrity of our healthcare infrastructure, along with cybersecurity in medical technology.
Key Takeaways:
- Cybersecurity in medical technology is now a critical aspect of patient safety, not just an IT concern.
- The opportunity for MedTech leaders lies not in reactive compliance but in building trust through certified, resilient devices from the start.
- AI-powered medical devices face specific security risks, such as dataset poisoning and model extraction, that conventional security systems weren’t designed to handle.
- Certification frameworks like IEEE 2621 turn cybersecurity from a compliance burden into a competitive advantage, signaling trust to regulators and clinicians.
- Smaller healthcare practices remain disproportionately exposed, but targeted initiatives, such as NHS England’s cyber resilience webinars, are closing the gap.
Understanding the Importance of Cybersecurity in Medical Technology
In recent years, the healthcare industry has become increasingly reliant on medical devices and systems, making cybersecurity an essential component of healthcare. Moreover, cyber-attacks on Protected Health Information (PHI), Personal Identification Information (PII), and other programs pose a risk to patient safety and privacy. Additionally, healthcare organizations possess a lot of information of high monetary and intelligence value to cyber thieves, making them particularly vulnerable and targeted by cyberattacks. Cybersecurity in healthcare ensures the privacy and safety of patients’ information for medical providers.
Global Cybersecurity Market in The Healthcare Sector 2023-2027
As of 2023, the global healthcare cybersecurity market has been valued at 20.1 billion U.S. dollars. This market is projected to experience substantial growth and is estimated to surpass 58 billion U.S. dollars worldwide by the year 2027.
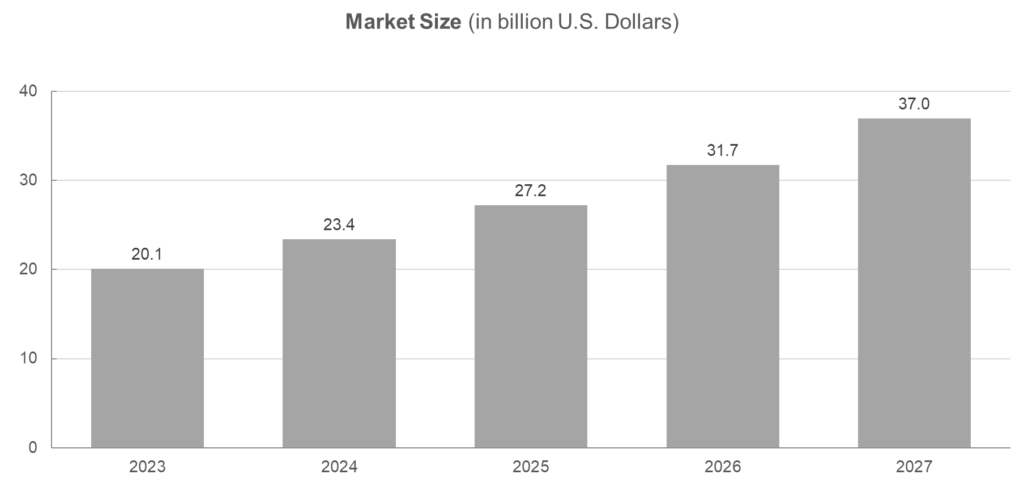
Figure 1: Global Cybersecurity Market in the Healthcare Sector 2023-2027
Key Market Players in the Cybersecurity Healthcare Market
Censinet, Cynerio, Virta Laboratories, Palo Alto Networks, Cisco, IBM, Claroty, Juniper, CrowdStrike, Check Point, Forescout, MedCrypt, Protenus, Zeguro, JFrog, Sophos, Kudelski Security, Trend Micro, Fortinet, Imprivata, Armis, Saviynt, Sophos, Forcepoint, Verimatrix, CloudWave, Sternum, Dell EMC, and others.
Common Cybersecurity Threats Faced By Healthcare Providers

Figure 2: Cybersecurity Threats Face In Healthcare
- Phishing: It is the most common cybersecurity threat in healthcare. It involves infecting a seemingly innocuous email with malicious links, compromising the integrity of systems and patients’ privacy.
- Ransomware: Ransomware is another common and expensive threat to healthcare organizations. It encrypts data and demands payment to restore access to it.
- Malware is software designed to harm or exploit any computer system. It can compromise system integrity and patient privacy.
- Insider Threats: Insider threats are cybersecurity threats involving contractors or employees who have access to sensitive information and use it for malicious purposes.
- DDoS Attacks: Distributed Denial of Service attacks are cybersecurity threats that involve overwhelming a system with traffic, making it unavailable to users.
- Cloud Threats: Cloud threats are a type of cybersecurity threat that involves exploiting vulnerabilities in cloud-based systems.
- Outdated Systems: Outdated systems are a type of cybersecurity threat that involves using outdated software or hardware no longer supported by the vendor, making them vulnerable to cyberattacks.
What are Specific Technologies Used for Ongoing Threat Detection in the Healthcare Sector?
- AI-Driven Behavioral Analytics: AI and Machine Learning (ML) are significantly changing treatment planning and diagnostics. However, demand for large datasets poses privacy concerns. Due to the ease of manipulation using an AI system, there is a risk of biased treatment plans and inaccurate diagnoses. Risk mitigation includes rigorous testing of AI systems for potential irregularities and ensuring patient data anonymity.
- Real-Time Security Information and Event Management (SIEM): Organizations within the healthcare ecosystem are at a consistent risk of malware attack. Hence, an integrated yet tailored solution is required. Malware threatens patient safety, and distributed denial-of-service (DDoS) attacks hinder patient care. Therefore, strong encryption and data monitoring protocols need to be embedded to ensure patient safety and strengthen patient privacy.
- Endpoint Detection and Response (EDR) & 24/7 SOC Monitoring: Continuous evaluation and monitoring of system logs, network traffic, and activities of users allows proactive threat recognition. It is essential for organizations to implement disaster recovery plans and redundant systems to protect patient care and prevent vital services from cyberattacks.
- Automated Vulnerability Scanning & IoMT Visibility Tools: Rise in IoT medical devices increased the number of entry points, thereby aggravating the cybercrime threats. Healthcare institutions collaborating with device manufacturers for embedding security measures in device design remain protected from cyber threats rooted in design or system vulnerabilities. Strict segmentation of device networks and continuous monitoring are critical safeguards.
Overall, MedTech firms embracing these technologies create the need to shift to unified platforms from standalone security products, as unified platforms offer proper visibility across device fleets. The FDA mandates manufacturers to consider cybersecurity in the product approval procedure, highlighting the significance of security in the safety of medical devices.
Enhancing Security Measures in Medical Technology
Enhancing security measures in medical technology is crucial to protect patient data and ensure patient safety. Here are some ways healthcare providers can improve the security of medical devices, such as automated diagnosis using AI, blockchain, IoT, and other smart devices :
- Ensure All Medical Devices have a Secure Password: Secure passwords should have at least eight characters and contain numeric, alphabetic, and special characters.
- IoT and Smart Devices: They are revolutionizing patient care, empowering patients to monitor their health with connected devices, while smart beds and medication dispensers enhance at-home care. Clinicians benefit from improved patient behavior monitoring. Healthcare transformed through IoT.
- Blockchain: It has revolutionized healthcare with improved data security, interoperability, and privacy. Also, streamlined electronic records, eliminated intermediaries, and enhanced identity management to drive innovation.
- Artificial Intelligence: Automated AI in healthcare improves outcomes with evaluated medical knowledge. It aids rapid diagnosis, offers affordable care, and prevents cybersecurity attacks.
- Follow FDA Guidelines: The FDA provides guidelines for medical device safety that can be a starting point for securing medical devices.
- Find Medical Device Cybersecurity Companies: They may include McAfee, Imprivata, Protenus, Check Point Software, Philips, GE Healthcare, Trellix, CrowdStrike, etc. They may help provide some solutions.
A Vision for Robust Medical Technology Cybersecurity
- Cybersecurity Investment: An integrated and robust cybersecurity framework in the medical technology sector is crucial for ensuring the safety and security of medical devices and protecting patients’ confidential data.
- Building Digital Resilience: Healthcare’s digital transformation requires a resilient ecosystem, focusing on securing medical devices and digitalization across institutions and healthcare delivery to counter cyber threats.
- Adopting Cybersecurity Frameworks: Healthcare organizations benefit from established frameworks like NIST CSF, helping bolster cybersecurity, complemented by other compliance efforts like HIPAA Security Rule.
- Securing Supply Chain: Ensuring medical device integrity throughout its lifecycle demands stringent supply chain security to mitigate vulnerabilities comprehensively.
- Continuous Assessment and Improvement: Regularly evaluating and improving security programs, roles, and responsibilities while prioritizing measures is vital to staying ahead of evolving cyber threats in healthcare organizations.
Real-time Monitoring for Swift Cybersecurity Threat Detection And Response
To implement real-time monitoring solutions for detecting and responding to cybersecurity threats promptly in the medical technology sector, the following steps can be taken:
- Embrace Cybersecurity Monitoring Tools: Employ real-time cybersecurity monitoring tools for network traffic, system logs, and user activities. Proactively detect unusual or malicious behavior.
- Automate Security Monitoring: Deploy automated systems for continuous network and endpoint security monitoring. Also, it swiftly detects and alerts cybersecurity teams about potential threats for rapid response and mitigation.
- Implement Real-time Data Monitoring: Establish capabilities for real-time data monitoring to track and manage organizational data access. In addition, it analyzes system event logs, user activities, and system access instantly to identify security threats as they occur.
- Deploy Threat Detection and Response Software: Utilize threat detection and response software with real-time monitoring. Additionally, it detects advanced attacks and receives customizable alerts for immediate response and incident management.
- Establish Continuous Monitoring and Analysis: Implement continuous monitoring and analysis to monitor the network and systems continuously. Moreover, regularly review security logs, analyze events, and conduct vulnerability assessments for proactive threat identification.
- Integrate with Incident Response Plan: Integrate real-time monitoring solutions with an incident response plan. In addition, ensure a predefined process for prompt and effective response to cybersecurity threats, including containment, eradication, and recovery procedures.
Cybersecurity in the Medical Technology: Collaboration in Healthcare

Figure 3: Cybersecurity Collaboration
- Identify Common Goals: Healthcare organizations, technology vendors, and cybersecurity experts should identify common goals and work together to achieve them.
- Share Information: Sharing information about cybersecurity threats and best practices can help improve medical technology’s overall security.
- Establish Clear Roles and Responsibilities: Establishing clear roles and responsibilities can help to ensure that everyone is working towards the same goal.
- Leverage Automation: Implementing security automation can significantly enhance the effectiveness and expediency of identifying and swiftly responding to potential threats.
- Develop a Cybersecurity Strategy: A comprehensive cybersecurity strategy can ensure all stakeholders are aligned and working towards the same goal.
- Train Employees: Training employees on cybersecurity best practices can help reduce the perils of human mistakes and improve overall security.
- Participate in Industry Groups: Industry groups can facilitate collaboration and information sharing between healthcare organizations, technology vendors, and cybersecurity experts.
Healthcare Cybersecurity Companies and Solutions in 2026
- Medical device security firms such as Claroty, MedCrypt, and others are experts in IoMT security. They offer adequate visibility, vulnerability management, and threat identification for clinical environments.
- Network security and segmentation providers like Forescout and Cisco have healthcare industry-specific offerings that separate medical devices from network traffic, which ultimately helps in decreasing the risk of unauthorized access.
- Trend Micro, CrowdStrike, and Fortinet deliver endpoint detection and response (EDR) built specifically for healthcare settings, adhering to FDA regulations and HIPAA.
- The IEEE Medical Device Cybersecurity Certification program, developed on the IEEE 2621 standards, provides a structured way for manufacturers to exhibit adherence to regulatory requirements comprising section 524B of the Federal Food, Drug, and Cosmetic Act and FDA cybersecurity guidance. Such testing guidelines and certifications help in minimizing cybersecurity risks in medical devices.
- Cybersecurity can serve as a value proposition rather than a cost driver. Medical devices that are IEEE 2621 certified earn the trust of patients and healthcare practitioners, delivering tangible benefits in healthcare markets, as credibility and safety influence buying decisions.
Cybersecurity for Optometrists and Small Healthcare Practices
Small healthcare practices, from optometry, pharmacy, and dentistry to general practice, encounter various cybersecurity risks. Small providers face budget constraints and limited IT resources while ensuring compliance with GDPR and HIPAA. Small practices tend to depend on connected systems that include telehealth platforms, digital imaging, and EHRs.
The National Institute of Standards and Technology (NIST) Cybersecurity Framework 2.0 renders a scalable approach that small and medium-sized practices can deploy incrementally for managing cybersecurity risks. Some basic measures consist of:
- Applying multi-factor authentication for all system access
- Carrying out employee cybersecurity training in a regular and consistent manner.
- Maintaining offline backups of crucial data
- Ensuring updated software and device firmware
- Setting an incident response plan
In the US, cyber liability insurance helps optometrists deal with the consequences of cybersecurity incidents and ensures effective cybersecurity risk management. Furthermore, NHS England plans to deliver cyber resilience webinars to healthcare professionals, including optometrists, to strengthen the security system.
Ethical Considerations in Data Privacy and Patient Consent
Ensuring data privacy and patient consent are critical ethical aspects of cybersecurity in medical technology. Here are the key findings:
Growing for-profit companies acquiring extensive healthcare system databases raise fresh hurdles in protecting patients’ privacy despite existing privacy laws in the United States.
- Sharing patient data with entities that could exploit it for commercial gain or target vulnerable populations raises significant ethical concerns
- Breaches in the confidentiality of extensive databases put millions of patients at risk of exploitation, necessitating new regulations to govern the sharing of patient data
- Addressing ethical considerations surrounding patient data contribution to research is crucial, especially when the potential for commercial exploitation exists by sharing patient data with third-party companies
- Privacy and confidentiality of personal information, including electronic medical records and genomic data, raise important ethical and regulatory considerations
- Obtaining informed consent becomes essential when using individuals’ health information for research, regardless of its direct relevance to clinical or insurance purposes
- Applying the respect principle for persons in health information research requires safeguarding patient privacy, dignity, and confidentiality while minimizing potential harm
- Regulations should prioritize patient agency, consent, and advanced data anonymization methods to address privacy concerns related to artificial intelligence
Conclusion
The healthcare industry faces heightened vulnerability to cyberattacks due to the abundance of valuable information, making it an attractive target for cybercriminals and nation-state actors seeking monetary gain or intelligence. While the primary objective of the healthcare and pharmaceutical sectors is to preserve lives and promote well-being, the digital age has brought about the computerization of personal and sensitive data. This digitization has facilitated easier access to information and drawn the attention of malicious individuals seeking to exploit vulnerabilities. Notably, biomedical devices are vulnerable to cyberattacks.
Establishing best practices for securing medical devices is crucial to ensuring comprehensive cybersecurity measures. One key step is to utilize inventory data to identify all devices within the healthcare system. Moreover, given the significant attention and investments in healthcare cybersecurity, it is essential to address the potential risk posed by disgruntled individuals who intentionally disclose patient information out of personal resentment or for illicit gains in the black market, where protected health information is in demand. Looking ahead, technology will continue to wield a significant influence in shaping the future of healthcare.
Stellarix is supporting MedTech organizations in navigating the intricate cybersecurity domain through its regulatory intelligence, R&D consulting, and strategic partner scouting services. Deep industry knowledge of our consulting experts, coupled with 16+ years of experience, helps clients address the most complex challenges through innovative solutions, turning market risks into opportunities.
Let's Take the Conversation Forward
Reach out to Stellarix experts for tailored solutions to streamline your operations and achieve
measurable business excellence.



